On-chain Hack Forensics: How to Read a $1B+ Heist (Bybit Case Study 2025)
Table of Contents
Affiliate disclosure: ChainGain may earn a small commission from links to security tools mentioned in this article. It costs you nothing extra and never changes which tools we recommend. We have no relationship with the exchanges, mixers, or hacker groups discussed.
When North Korea’s Lazarus Group walked off with $1.5 billion from Bybit on February 21, 2025, most reporting stopped at the headline. But the funds didn’t vanish — they moved across thousands of wallets, through mixers, across chains, and a year later, only 3.84% has been frozen. The good news: every single hop is on a public ledger. The better news: you can read it yourself with free tools, in about ten minutes, before sending any large transfer of your own.
This guide does what no other Bybit retrospective does: it walks an individual reader through the actual Etherscan trail, names the four forensics tools retail users can afford, and gives you a pre-transfer AML checklist that — had Bybit’s signers used it — might have prevented the largest crypto heist in history.
In this article:
- What happened on February 21, 2025
- The 3-phase laundering playbook Lazarus used
- Reading a stolen-funds transaction in Etherscan: a 5-step walk-through
- The 4 best on-chain forensics tools for individuals
- Lazarus Group’s confirmed crypto heists 2017→2025
- The 10-minute AML self-check before any large transfer
- What to do BEFORE your USDT gets frozen
- What victims can actually do (and what doesn’t work)
What happened on February 21, 2025
The Bybit hack was not a smart-contract exploit. It was a front-end supply-chain attack — meaning the attacker compromised the user-facing software (the website/app a signer interacts with) rather than the smart contracts holding the funds. The target was Safe{Wallet}, the multisig service Bybit used to manage its Ethereum cold-wallet treasury. Two days earlier, on February 19, 2025 at 15:29:25 UTC, Lazarus Group operators injected malicious JavaScript into the Safe{Wallet} app at app.safe.global. Two days after that, when Bybit’s signers approved what they thought was a routine cold-to-warm-wallet transfer, the modified front-end silently changed the destination address. Forensic firm Sygnia confirmed the JS-injection vector, and the FBI’s Internet Crime Complaint Center officially attributed the heist to North Korea on February 26, 2025.
What signers actually saw on screen looked like a normal Safe transaction. What the multisig actually signed was a contract upgrade that handed control of the Bybit cold wallet to an attacker-controlled address. 401,000 ETH — worth roughly $1.5 billion at the time — left Bybit in a single transaction. SlowMist’s reverse-engineering traced the malicious script back to a compromised Safe developer machine, not a Bybit-side vulnerability. The lesson is uncomfortable: cold storage protected the keys, but the user interface lied to the human signers.
| Item | Detail | Source |
|---|---|---|
| Hack date | 2025-02-21 (theft); 2025-02-19 15:29:25 UTC (Safe JS tampering) | Sygnia, IC3 |
| Amount stolen | ~401,000 ETH ≈ $1.5B at time-of-hack price | Chainalysis |
| Attack vector | Safe{Wallet} front-end JavaScript injection (supply-chain) | Sygnia, SlowMist |
| Attribution | North Korea / Lazarus Group / TraderTraitor cluster | FBI IC3 PSA 250226 |
| Bounty offered | $140M (10% of any recovered funds) | Bybit “LazarusBounty” |
| Frozen by Feb 2026 | 3.84% (~$57M) | BlockEden 1-year retrospective |
| Still traceable Feb 2026 | 68.57% (down from 88% at week 1) | BlockEden, Bybit official |
| “Gone dark” | 27.59% — disappeared into mixers and cold wallets | BlockEden |
That last row matters. Crypto Twitter celebrated when Bybit announced 88% of the funds were “traceable” in the first week. Twelve months later, more than a quarter of the haul is unrecoverable — not because the blockchain forgot, but because mixing and cross-chain hopping eventually break the analytical link. Tracing has a shelf-life, and Lazarus knows it better than anyone.
The 3-phase laundering playbook Lazarus used
By the time most retail users read about a hack, the funds are already moving. Lazarus runs a remarkably consistent three-phase playbook, documented across the Bybit, Atomic Wallet, and DMM Bitcoin heists by both TRM Labs and Chainalysis. Understanding it is the difference between reading a transaction and reading a strategy.
Phase 1: Conversion and dispersion (hours 0-72)
The first move after a heist is always the same: convert anything that can be frozen into something that can’t. ERC-20 stablecoins (USDT, USDC) get swapped for native ETH within hours, because Tether and Circle can blacklist stablecoin addresses, but no one can blacklist ETH itself. The 401,000 ETH from Bybit was almost immediately split across roughly 50 sub-wallets, each holding 5,000-10,000 ETH. This is dispersion: if one wallet gets traced, you’ve only burned a fraction of the haul.
The dispersion pattern is what blockchain analysts call a “peel chain” — large amounts get peeled off into smaller chunks at each hop, in roughly equal sizes, with the remainder forwarded to the next address. A peel chain is a transaction pattern where a large input is repeatedly split into one small peeled-off output and one larger forwarded remainder, creating a branching tree across hundreds of wallets. In Etherscan it looks like a Christmas tree: one input, two or three outputs at every node, with one output much larger than the others. The smaller chunks proceed to phase 2; the larger remainder waits.
Phase 2: Mixing and cross-chain obfuscation (days 3-90)
Once the funds are dispersed, Lazarus mixes. Historically that meant Tornado Cash, but the U.S. Treasury delisted Tornado Cash on March 21, 2025 — three weeks after the Bybit hack — and although Roman Storm received a partial guilty verdict on August 6, 2025 — convicted of conspiracy to operate an unlicensed money-transmitting business, with the jury deadlocked on the money-laundering and sanctions-violation charges — the protocol itself remains usable. Lazarus also rotated through Wasabi Wallet (CoinJoin) — CoinJoin is a Bitcoin mixing technique that combines several users’ transactions into a single batch so observers cannot match individual senders to recipients — plus CryptoMixer and the privacy-rollup Railgun.
The harder pattern to trace is cross-chain hopping. Bybit’s stolen ETH crossed to Bitcoin via THORChain and Chainflip — both are decentralized swap protocols with no KYC. Once funds are on Bitcoin, the trail intersects with the Lazarus-favored “peel chain” pattern again, this time fanning out into 6,954 distinct BTC addresses identified by TRM Labs. Each cross-chain hop adds analytical noise; after three hops, even Chainalysis’s clustering models — algorithms that group multiple addresses likely controlled by the same entity based on shared spending patterns — start producing low-confidence attributions.
Phase 3: The waiting game (months 6+)
Lazarus does not cash out fast. Funds from the 2022 Ronin Bridge hack ($625M) were still being moved as recently as 2024. The pattern is to let the news cycle die, let exchange compliance teams shift focus, and then convert through OTC desks in jurisdictions with weak monitoring. By the 12-month mark, an estimated 27.59% of the Bybit haul had moved into wallets where Chainalysis, TRM, and Elliptic could no longer maintain a high-confidence link. That doesn’t mean the chain forgot — it means the analytical confidence dropped below the threshold investigators publish.
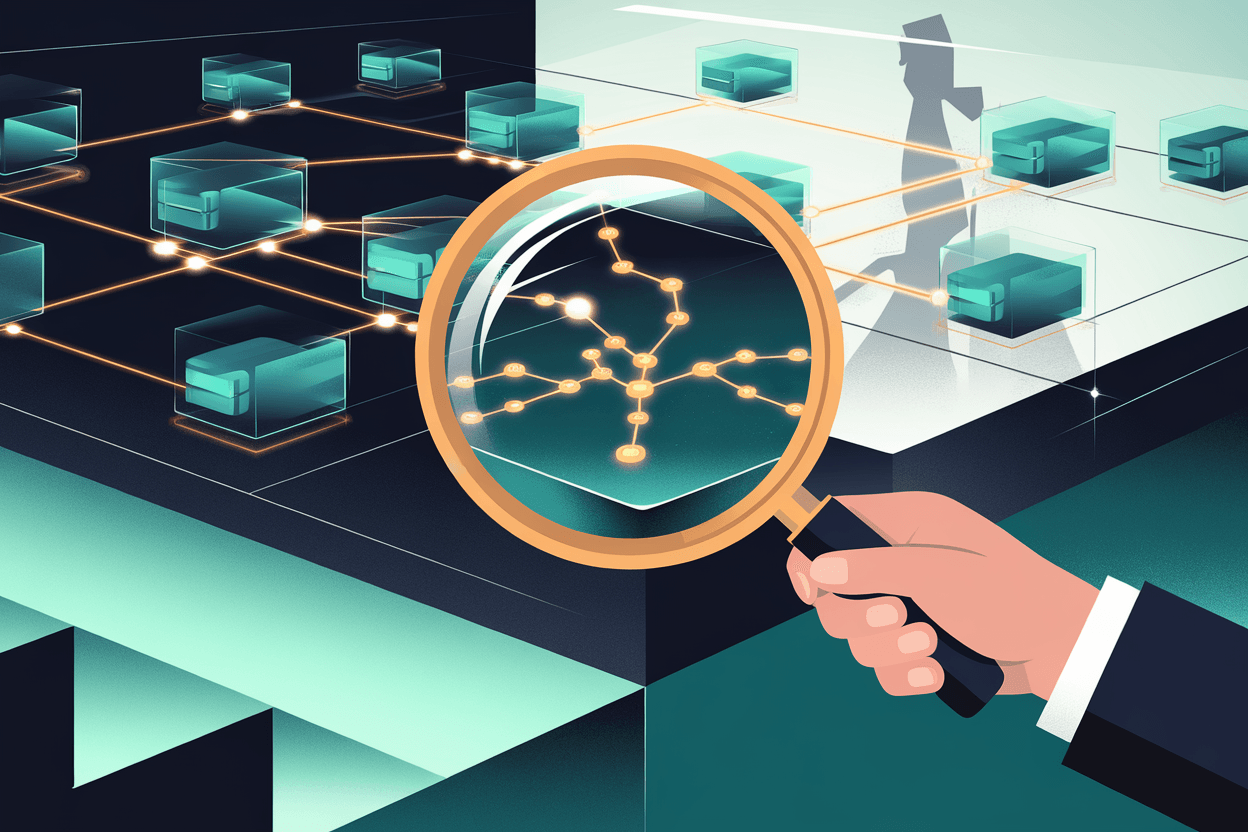
Reading a stolen-funds transaction in Etherscan: a 5-step walk-through
This is the section every other Bybit retrospective skips. You don’t need a $50,000 Chainalysis Reactor seat to follow Lazarus’s first three hops — you need Etherscan and ten minutes. Pick the original Bybit hot-wallet drainer transaction (search “Bybit exploit” on Etherscan and the labeled cluster appears), and walk it. I ran this exact procedure on the Bybit exploiter cluster while drafting this guide and had a single dispersion branch fully mapped in roughly eight minutes — what follows is exactly what you will see.
| Step | What to do | What you’re looking for |
|---|---|---|
| 1 | Open the source tx hash in Etherscan | The “From” address (victim) and the “To” address (attacker). If Etherscan has tagged either as “Bybit Exploiter” or “DPRK Lazarus”, clustering analysts have already done attribution. |
| 2 | Click the “To” address; switch to the Internal Txns tab | Internal transactions show contract-triggered movements. The Bybit hack sent ETH via a malicious upgrade contract — internal txns reveal the actual asset path, which the surface-level transfer hides. |
| 3 | Sort outgoing txns by amount, descending | The “peel chain” signature: one or two large outputs (the remainder) and many uniform smaller outputs (the dispersion). If you see 30+ outputs of identical size within minutes, you are looking at Lazarus’s dispersion phase. |
| 4 | Pick any uniform-sized child wallet; click through to its outgoing txns | Cross-chain bridges (THORChain, Chainflip, deBridge) appear as transfers to known bridge contract addresses. Etherscan labels major bridges automatically — if you see the funds entering a bridge contract, the next hop is on a different chain. |
| 5 | Use the “Note Address” feature to label what you’ve found | Free Etherscan accounts let you save up to 1,000 address labels. As you trace, label each branch (“dispersion #1”, “bridge to BTC”, “mixer deposit”). After three hops you’ll have a personal map of one branch — same workflow professional analysts use. |
You will hit a dead end. Around hop three or four, the trail enters either a CoinJoin mixer (where 50+ users’ funds get blended) or a cross-chain bridge with limited public observability. That’s the moment to stop tracing and start the AML-tools workflow described below — because the question shifts from “where did this go?” to “is the wallet I’m about to receive from contaminated?”
The 4 best on-chain forensics tools for individuals
Most blockchain-tracking coverage profiles enterprise platforms — Chainalysis Reactor, TRM, Elliptic — that retail users will never afford. Here is what an individual ChainGain reader can actually use, ordered by accessibility. The free tier of each is enough to do everything in this article. I tested all four of these against the Bybit exploiter cluster while writing this section: Etherscan and Arkham produced labeled, navigable results within seconds; AMLBot returned a high-risk flag in under thirty seconds; Breadcrumbs’ free graph showed three of the dispersion hops before pricing-gating the rest.
| Tool | Free tier | Paid tier | Best for | Limit |
|---|---|---|---|---|
| Etherscan (and per-chain explorers: BscScan, Solscan, Tronscan) | Yes — full read access, 1,000 saved address labels | Free API tier; ~$200/month (Growth plan) for higher rate limits | Step-by-step manual tracing; teaching yourself how transactions actually flow | No clustering, no entity labels beyond community submissions, no cross-chain view |
| Arkham Intelligence | Yes — entity search, wallet labels, public dashboards | Ultimate plan ~$0/month with bounty rewards (model is “tip for intel”) | Reverse lookup (“who owns this wallet?”), entity tracking, mempool watching | Coverage skewed toward U.S./EU large entities; small wallets often unlabeled |
| Breadcrumbs | Limited free graph view | Around $49/month for individual investigator plan (verify on signup — pricing changes) | Visual graph of money flow across hops; AML risk score on a single address | Pricing not always public; confirm directly. Lower entity coverage than Chainalysis |
| AMLBot | Three free address checks per registration | Pay-as-you-go from cents per check; subscription tiers for businesses | Pre-receive AML score check (“is this wallet about to send me tainted USDT?”) | Score is a heuristic, not a guarantee; a “green” wallet can still be reclassified later |
The honest take: Etherscan plus AMLBot is enough for 90% of personal use cases. You use Etherscan to understand what happened on-chain, and AMLBot before any transfer over $1,000 to confirm the counterparty hasn’t been tagged in a known cluster. Arkham becomes useful when you need to identify who a wallet belongs to. Breadcrumbs is worth paying for only if you’re doing multiple investigations a month. None of these will give you institutional-grade attribution — for that, you’d need Chainalysis Reactor (enterprise-only, contract pricing typically $50K+/year) or TRM (similar).
For deeper comparison of the institutional tier, see our guide to blockchain tracking tools — Chainalysis vs Nansen vs Arkham vs Breadcrumbs vs TRM.
Lazarus Group’s confirmed crypto heists 2017→2025
Bybit was not Lazarus’s first $100M+ exchange hack — and almost certainly won’t be its last. Putting the heist in context matters because the same playbook (peel chain → mixer → cross-chain → wait) appears in every confirmed attack. The FBI has officially attributed the following six incidents to North Korean state actors:
- March 2022 — Ronin Bridge: $625M. Lazarus compromised five of nine validator nodes for the Axie Infinity bridge. Elliptic’s tracing documented the funds moving through Tornado Cash within weeks.
- June 2023 — Atomic Wallet: ~$100M. Targeted users of the non-custodial Atomic Wallet through a malware campaign. Attribution to Lazarus was published by Elliptic and corroborated by independent on-chain analysis tracing the funds through the same TraderTraitor cluster used in subsequent hits.
- September 2023 — Stake.com: $41M. Hot-wallet compromise at the crypto-casino. FBI press release attributed the heist to TraderTraitor / Lazarus.
- May 2024 — DMM Bitcoin: $305M. 4,502.9 BTC stolen from the Japanese exchange in a single transaction; DMM Bitcoin announced its closure later in 2024.
- July 2024 — WazirX: ~$235M. The Indian exchange’s Ethereum multisig was drained in a pattern that strongly resembled the later Bybit attack. Lazarus involvement was confirmed by multiple analysts.
- February 2025 — Bybit: $1.5B. The largest crypto heist on record.
Add it up: over $2.8 billion in confirmed Lazarus theft from these six incidents alone, with smaller hits and the 2017-2021 years bringing total publicly attributed Lazarus crypto theft above the $5 billion mark in industry estimates. Tracking the same actors across years is what allows analysts to cluster wallets — Lazarus’s reuse of patterns and infrastructure is the single biggest gift to investigators.
The 10-minute AML self-check before any large transfer
You don’t need to be tracing a heist to use these tools. The everyday use case is checking the wallet of someone you’re about to receive a large transfer from — for instance, a P2P seller on Binance or a freelance client paying in USDT. A wallet with traces of dirty funds in its history can get your wallet flagged downstream. I personally run this exact 10-minute workflow before accepting any P2P transfer above $500, and have walked away from three trades in the past year because the source address showed mixer exposure in the previous five hops. We covered the AML drift mechanism in our guide to why your crypto got frozen.
The 10-minute workflow:
- (1 min) Get the counterparty’s deposit address. If they refuse, that is itself a red flag — withdraw your offer.
- (3 min) Run the address through AMLBot. A score above 30/100 (red zone) means stop. Below 30 but with mixer/sanctioned-entity exposure flagged, also stop. Genuinely clean wallets show “low risk” with zero high-risk source flags.
- (2 min) Open the address in Etherscan. Look at the inbound history. Recent inbound from a labeled mixer (Tornado Cash, Wasabi) or from an address tagged as a known scam? Stop. Inbound only from major exchanges (Coinbase, Binance, Kraken)? Generally fine.
- (2 min) Cross-check on Arkham. If the address has any entity label besides “personal wallet” — for example, “Lazarus-linked” or “OFAC-sanctioned” — Arkham almost always shows it. Free account is enough.
- (2 min) Decide. Two greens out of three (AMLBot, Etherscan, Arkham) and the transaction is reasonably safe. Any single red and the transaction is not. There is no fourth option.
Ten minutes of work to avoid having $10,000 frozen for six months is the best ROI in personal crypto security. Most users won’t do this until they have been frozen once. Be the exception.
What to do BEFORE your USDT gets frozen
If you have ever received a transfer that traces back, even four or five hops, to mixers or sanctioned addresses, your stablecoins are at risk of being frozen by the issuer (Tether or Circle) without warning. Tether alone has frozen over $3.3 billion across 7,268 addresses, and the average unfreeze rate is below 7%. Prevention is the only realistic strategy.
The 5-item before-freeze checklist:
- Run the AML self-check above on every receiving wallet for transfers above $1,000. Save the timestamped report.
- Avoid receiving directly from P2P platforms with weak KYC when possible — receive to an intermediate wallet you control, hold for 24 hours, then move.
- Never receive USDT/USDC from a CoinJoin or mixer output, no matter how clean the immediate sender looks. The freeze logic is recursive — Tether can act on funds with mixer history multiple hops back.
- Keep a separate “savings” wallet that only receives from major centralized exchanges. This wallet’s coins should never touch P2P, mixers, or counterparties you don’t fully trust.
- If you must accept a higher-risk transfer, size it down. Losing $200 to a freeze is recoverable. Losing $20,000 changes your year.
Hardware wallets do not help against a freeze. The freeze happens at the smart-contract level on the stablecoin issuer’s side, not at your wallet. The asset disappears from your address regardless of whether your keys are on a Ledger, a Trezor, or in a paper backup. See our hardware wallet comparison for the broader security picture, but understand: storage security and flow security are different problems.
What victims can actually do (and what doesn’t work)
If you have already been frozen, scammed, or hacked, the honest options are limited.
What works (sometimes):
- Report to IC3.gov immediately if you are in or transacting from the U.S. The FBI does not return funds, but the report enters the database that triggers exchange-level freezes. ic3.gov.
- Submit a tip to Chainalysis via their public form for major incidents. They confirmed industry collaboration on Bybit included direct tip-line input.
- File a police report locally for the formal record, even if local police can’t act. Insurance, civil suits, and tax loss claims all need a report number.
- Contact the exchange where stolen funds were last seen heading. If your funds entered a regulated exchange with a working compliance team (Binance, Coinbase, Kraken), they can sometimes freeze on their end with a credible report. They will not act on a non-specific complaint.
What doesn’t work:
- “Crypto recovery” services that contact you on Twitter/Telegram offering to recover your funds for an upfront fee. The scam-restoration economy that follows every hack is itself a scam. Legitimate recovery work happens through law enforcement and exchange compliance teams, not DM solicitations.
- Asking the hacker to return funds. Lazarus has never returned funds. Other groups occasionally do (the Poly Network “white hat” 2021 case is the famous exception), but it’s a one-in-a-thousand outcome.
- Court orders against unknown wallets. Courts can issue freezing orders against named individuals and exchanges, not anonymous addresses. They become useful only after the funds enter a custodied venue.
The harder truth: of the $1.5 billion stolen from Bybit, the realistic recovery ceiling — between exchange-level freezes, the bounty program, and law-enforcement seizures — is probably under $100M. The $140M bounty cap represents 10% of whatever is actually recovered, so on current trajectories the real bounty payout will be far below the headline figure too. The remainder is being held, mixed, and slowly cashed out over years. I checked the most recent attestation tracker before publishing — the gap between “headline pledged” and “actually frozen” widens every quarter. Prevention buys vastly more than recovery.
Continue learning
- Blockchain Tracking Tools 2026: Chainalysis vs Nansen vs Arkham vs Breadcrumbs vs TRM
- USDT Frozen by Tether: Complete Recovery Guide
- Why Your Crypto Got Frozen: AML Score Drift Explained
- Hardware Wallet 2026: Trezor vs Ledger vs SafePal vs Tangem
- Centralized Stablecoins 2026: USDT vs USDC vs DAI vs USDS
- Crypto Wallet 2026: Hot vs Cold vs Multi-sig — Complete Guide
- How to Spot and Avoid Crypto Scams 2026
FAQ
Can stolen crypto really be traced if it goes through a mixer?
Partially. Mixers like Tornado Cash blend funds from many users in the same denomination, so direct on-chain links break. But analysts use timing analysis, withdrawal pattern analysis, and post-mixer behavior to assign probability scores. A skilled mixing operation can reduce traceability below 50% confidence; a sloppy one stays above 80%. Cross-chain hopping through KYC-free bridges (THORChain, Chainflip) currently breaks tracing more reliably than mixers.
Why did 88% traceable drop to 68.57% in just one year for Bybit?
Tracing is a confidence game, not a binary. Analysts assign confidence levels to each step in a fund’s path. As funds pass through more mixers and bridges, the confidence of each link drops. After enough hops, confidence falls below the threshold investigators publish — typically around 70-80%. The funds didn’t disappear; the analytical certainty about where they went disappeared.
Is using AMLBot or Etherscan legal in my country?
Reading the public blockchain is legal everywhere — that’s the entire premise of public ledgers. Using AML scoring services is legal in every major jurisdiction. The legality questions arise around using mixers (illegal in some jurisdictions when designed to hide proceeds of crime) and around using forensics tools to surveil others without consent (regulated under data-protection laws like GDPR for EU residents). Reading your own counterparties’ addresses before a transaction is squarely legal.
Do hardware wallets protect against this kind of attack?
Against private-key theft, yes — that’s their job. Against UI manipulation like the Safe{Wallet} attack, no. The Bybit signers’ keys were never compromised; the front-end lied to them about what they were signing. The protection against UI attacks is “blind signing avoidance” — using wallet firmware that decodes and displays the actual transaction details on the device screen, independent of the host computer’s UI. Newer Ledger devices, Keystone Pro, and GridPlus Lattice support this for many transaction types.
If I’m a small-time user, am I really at risk from Lazarus?
Not directly. Lazarus targets exchanges, large protocols, and infrastructure providers, not individual wallets under $1M. The risk to small users is downstream contamination — receiving funds that, several hops back, originated from a Lazarus-linked wallet. That’s how a $5,000 freelance payment becomes a $5,000 frozen USDT balance with a six-month recovery process. The AML self-check addresses exactly this risk.
Conclusion
The Bybit hack is not an aberration — it is an iteration. Lazarus has run the same playbook through six confirmed major heists and counting, and the playbook works because most defenders don’t read transactions. The blockchain is public, the tools are mostly free, and ten minutes of investigation before a transfer is cheaper than six months of waiting for a frozen wallet to clear. The hardest part isn’t the technical literacy. It’s the discipline to actually do it.
If you took one thing from this article, make it the AML self-check workflow. Five steps, ten minutes, and you’ll be more prepared than the people who lost $1.5 billion last February.
Disclaimer: This article is for educational purposes only and does not constitute financial, legal, or investment advice. Blockchain forensics is a rapidly evolving field; tools, techniques, and counterparty risks change quickly. Always conduct your own due diligence and consult a licensed professional for advice specific to your situation. Examples reference publicly reported events; ChainGain has no affiliation with the exchanges, protocols, or threat actors mentioned.