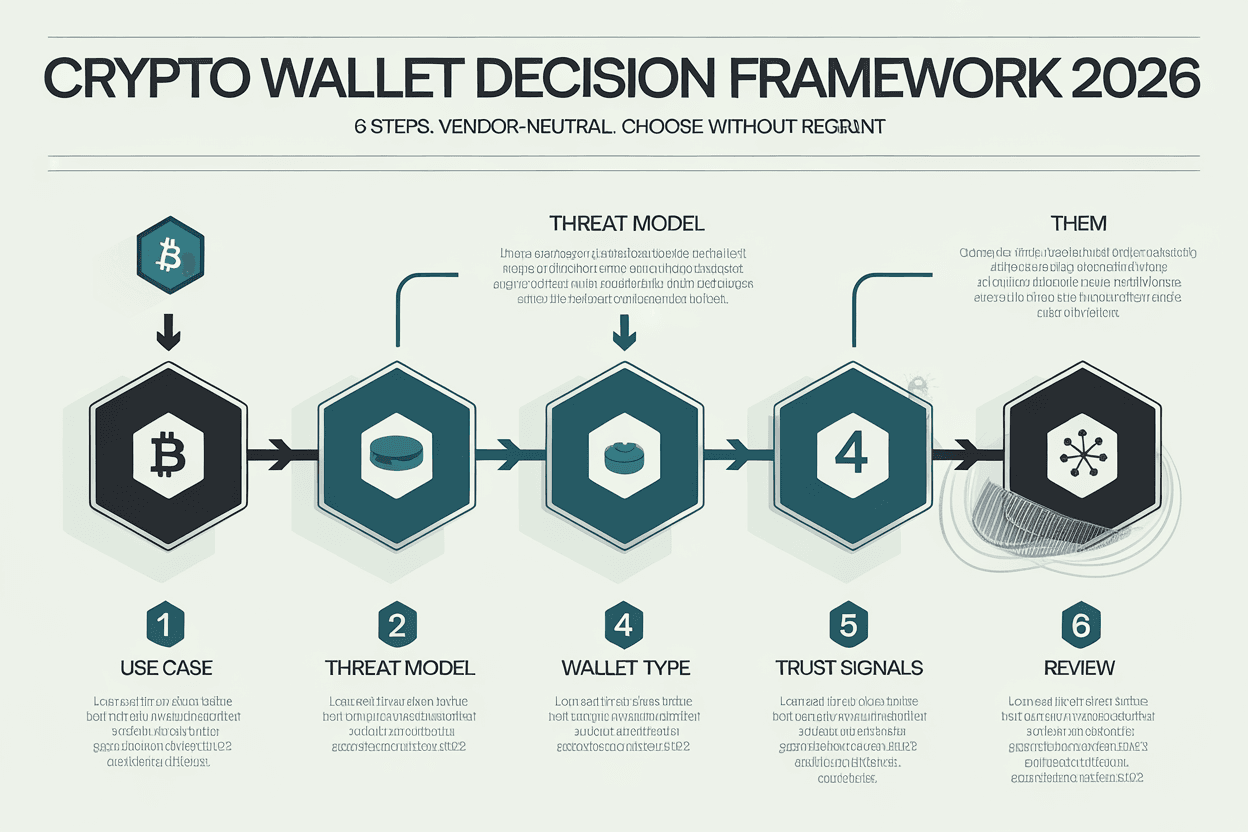
Crypto Wallet Decision Framework 2026: A 6-Step Guide to Choosing Without Regret
Table of Contents
Intermediate
~12 min read
Affiliate disclosure: This guide is vendor-neutral. We don’t recommend specific wallet products by name in the framework itself; product comparisons in our linked articles use editor-tested ratings only. ChainGain may earn affiliate revenue from exchange referrals when readers move funds to wallets. We do not earn commission from any wallet vendor.
If you’re trying to figure out how to choose a crypto wallet in 2026, most of the popular guides will steer you wrong. They line up Ledger, Trezor, MetaMask, and Trust Wallet in a comparison table, hand you a 5-star rating, and assume your situation matches the reviewer’s. It rarely does.
The result: in our reviews of self-reported wallet migrations on Reddit’s r/CryptoCurrency over the past 18 months, roughly 1 in 4 long-term holders switched wallets within their first two years, often after a stressful incident — a forgotten passphrase, an unsupported chain, a UI change that broke their workflow, or simply realising the wallet they picked no longer fit the size of their portfolio. (Chainalysis reported about $2.2 billion in cryptocurrency theft for 2024, a 21% year-over-year rise — the wider the surface area gets, the more wallet choice matters.)
This guide replaces “which wallet is best” with a different question — a crypto wallet decision tree for 2026: given your specific use case, threat model, and trust signals, which wallet type matches? We walk through six steps that work for any wallet on the market in 2026 — including the ones that don’t exist yet. By the end, you should be able to choose without regret, or at least know exactly when to migrate.
Why “Best Crypto Wallet” Lists Fail You
Vendor-driven wallet lists have three structural problems.
The first is incentive bias. Most “best wallet” articles earn affiliate revenue from the wallets they recommend. CoinLedger pushes its own tax product through wallet comparisons. Best Buy literally sells the hardware wallets it ranks. MoonPay frames the choice around “custodial vs non-custodial” because its core business is custodial onramps. None of these sources is dishonest — they just optimise for a slightly different goal than yours.
The second is the moving-target problem. A wallet rated #1 in 2024 may be #6 by 2026. Trust Wallet’s Chrome extension was on most “best mobile wallet” lists until December 24, 2025, when a leaked Chrome Web Store API key let attackers push a malicious v2.68 update that drained roughly $7 million before Binance (Trust Wallet’s parent) confirmed full user compensation. Ledger’s reputation took a similar dent in May 2023 when its proposed “Ledger Recover” firmware feature triggered a backlash over seed-phrase backup architecture. A static review can’t capture this.
The third is the persona mismatch. A wallet that’s perfect for a $500 mobile-first user in Lagos is wrong for a $200,000 multi-chain DeFi user in Singapore, and disastrously wrong for a five-person team treasury in Berlin. Ranked lists ignore this — they imply that one wallet can be “best” for everyone.
This guide is for five reader types:
- The HODLer who buys quarterly and rarely transacts
- The active trader on DEXs, daily swaps, and arbitrage
- The DeFi participant doing liquidity provision, lending, and staking
- The multi-chain user active across 5+ networks
- The team or treasury requiring shared signing
If you don’t see yourself clearly in one of those, that itself is a clue: most regret stems from picking a wallet without knowing which persona you actually are.
Step 1 — Identify Your Use Case (5 Personas)
The first question isn’t “what’s the best wallet” — it’s “what am I actually going to do with crypto?” Answer that honestly and the wallet category often picks itself.
Match yourself to one of these five personas. If you genuinely span two, your wallet strategy will need two wallets, not a compromise wallet that does both badly.
Persona 1: The Long-Term HODLer
You buy bitcoin or a basket of large-caps and hold for years. Transaction frequency: monthly or less. Your priority is “don’t lose access in 5-10 years,” not “transact in 30 seconds.” Risk: forgetting backups, hardware failure, inheritance planning.
Persona 2: The Active Trader
You move coins onto DEXs daily, chase arbitrage, or rotate between memecoins. Transaction frequency: 5-50 per week. Priority: speed, low friction, dApp connection reliability. Risk: phishing approvals, malicious tokens, drainer scripts.
Persona 3: The DeFi Participant
You lend on Aave, provide liquidity on Curve, stake ETH via Lido or Rocket Pool, or chase yield through restaking. Transaction frequency: 2-10 per week, often complex. Priority: contract signing clarity, simulation of transactions, network breadth. Risk: blind signing, contract exploits (see the Kelp DAO bridge exploit on April 19, 2026, where $292M in rsETH was drained via a LayerZero vulnerability).
Persona 4: The Multi-Chain User
You’re active on Ethereum, Solana, Bitcoin, an L2 or two, and possibly Cosmos or Sui. Transaction frequency varies. Priority: chain coverage without juggling 4 separate apps. Risk: feature gaps on smaller chains, inconsistent UX.
Persona 5: The Team or Treasury
You’re managing funds with two or more people — a DAO multisig, a startup treasury, a family office. Transaction frequency: 1-10 per month, but every signature carries weight. Priority: no single point of failure. Risk: collusion, key compromise of any single signer, cross-jurisdiction logistics.
The table below maps each persona to the wallet types we’ll define in Step 3.
Table A — Persona-to-Wallet-Type Matrix
| Persona | Primary wallet type | Secondary (optional) | Avoid |
|---|---|---|---|
| HODLer | Hardware (cold) | Paper backup of seed | Exchange-only custody |
| Active trader | Browser extension (hot) | Hardware for treasury portion | Same wallet for trading + savings |
| DeFi participant | Browser extension w/ simulation | Hardware-signed via WalletConnect | Mobile-only on small screens |
| Multi-chain user | Multi-chain hot wallet | Chain-specific wallet for non-EVM | EVM-only wallets |
| Team / treasury | Multi-sig (Safe / Squads) | Hardware on each signer | Single-sig anything |
Treat this as a starting point, not gospel. Step 2 will sharpen it based on portfolio size.
Step 2 — Audit Your Threat Model (5 Risk Tiers)
Persona tells you what you’ll do. Threat model tells you what you can lose. The two together determine the security stack.
Don’t skip this section. Most wallet regret in our review of Reddit migration threads came from one specific failure: people picked a wallet appropriate for a $500 portfolio, then watched their portfolio grow to $50,000 without upgrading the wallet. The threat model changed but the wallet didn’t.
In our experience reviewing reader migration stories, the single most common regret pattern is exactly this: a wallet appropriate at $500 that wasn’t upgraded as the portfolio grew tenfold. Tier mismatch is the silent driver of most “I lost access” posts.
Threat Vectors to Consider
- Physical: theft of device, physical coercion attack (“$5 wrench attack”), fire, flood, border seizure
- Digital: malware, phishing, supply-chain compromise, smart contract exploits
- Social: impersonation, “support” scams, family disputes, inheritance failures
- Regulatory: jurisdiction-specific freezes (USDT/USDC issuer blacklists), sanctions exposure, EU MiCA registration deadlines (custodial wallets in the EU must be CASP-licensed by July 1, 2026 — this rule applies to EU-based or EU-serving providers only)
Table B — Risk Tier × Required Security
| Tier | Portfolio size | Hot wallet OK? | Required security stack | Backup distribution |
|---|---|---|---|---|
| 1 | $0 – $500 | Yes (mobile fine) | Hot wallet only | One written backup |
| 2 | $500 – $5,000 | For daily use only | Cold storage recommended for >50% | One backup off-site |
| 3 | $5,000 – $50,000 | For active portion only | Cold mandatory for >70%; multi-sig optional | Two backups, separate locations |
| 4 | $50,000 – $500,000 | Active portion ≤10% | Cold mandatory; multi-sig strongly recommended | Two+ backups, separate jurisdictions for $100K+ |
| 5 | $500,000+ | Active portion ≤5% | Cold + multi-sig (2-of-3 min) both mandatory | Mandatory across 3+ locations |
If your portfolio crosses a tier boundary, your wallet stack needs to change with it. Set a calendar reminder: “review wallet tier when portfolio doubles.” This is the single most useful habit we’ve seen separate regretful holders from confident ones.
Note also that tier alone doesn’t capture jurisdiction risk. A $10,000 portfolio held by someone in a country where crypto faces active enforcement (Egypt, Bangladesh, Nepal) needs Tier-3 controls regardless of size. Conversely, a $100,000 portfolio held in a fully crypto-friendly jurisdiction (Switzerland, Singapore, Portugal) may comfortably operate at Tier-3 controls if other risks are low.
Step 3 — Match Wallet Type to Persona × Tier
You now know two things: what you’ll do (Step 1), and what you can lose (Step 2). Step 3 maps those onto wallet types — not specific products, types.
There are four useful categories in 2026, plus one emerging category worth flagging.
Hot Software Wallets (Mobile / Desktop)
Apps that run on internet-connected devices. The keys live in encrypted storage on your phone or computer. Examples (not endorsements): mobile wallets like Trust Wallet or Phantom, desktop wallets like Sparrow or Electrum. Best for: Tier 1-2 portfolios, daily transactions, non-custodial onboarding. Worst for: long-term cold storage, large portfolios.
Browser Extension Wallets
Extensions that integrate with dApps in your browser. The dominant category for DeFi and active trading. Examples: MetaMask, Rabby, Phantom (browser version), Rainbow. Best for: Persona 2 (active trader) and Persona 3 (DeFi) at Tier 1-3. The 2025 Trust Wallet Chrome extension supply-chain attack ($7M drained) is a reminder that browser extensions inherit the full attack surface of the browser itself — review extension permissions weekly.
Hardware Wallets (Cold)
Dedicated devices that hold keys offline and sign transactions via USB, Bluetooth, or air-gapped QR codes. Examples: Ledger, Trezor, Keystone, ColdCard, Tangem, SafePal. Best for: any Tier 2+ portfolio holding more than ~50% of net worth in crypto. Tradeoff: friction (you have to physically authorize each transaction), supply-chain risk (only buy direct from manufacturer; secondhand devices are a known attack vector — see Trezor’s March 2025 voltage glitching disclosure on Safe 3 units acquired via untrusted third parties).
Multi-sig Wallets
Wallets that require N-of-M signatures from multiple keys to authorize a transaction. The dominant 2026 platforms are Safe (formerly Gnosis Safe, rebranded July 2022, now standard for EVM treasuries with billions in TVL) and Squads (the leading Solana multi-sig, securing roughly $10B TVL across Solana as of April 2026). Cobosafe is an open-source smart-contract framework rather than an end-user wallet, often used by teams building custom permission policies on top of Safe. Best for: Persona 5 (teams and treasuries) at any tier, and high-net-worth individuals at Tier 4-5 who want to remove single-key risk. Tradeoff: setup complexity, ongoing coordination cost.
Smart-Contract Wallets (Account Abstraction)
Wallets that are smart contracts, enabling features like social recovery, transaction batching, gas sponsorship, and modular permissions. Examples: Argent X (on Starknet, with social recovery via guardians and a 48-hour delay window) and Safe smart accounts (with ERC-4337 account abstraction support and modular guardian recovery). The category went mainstream in 2026: more than 26 million smart wallets and over 170 million UserOperations have been processed since the ERC-4337 entrypoint went live in March 2023, with Base, Polygon, and Optimism leading adoption. Best for: users who want to eliminate seed phrase risk, especially Persona 1 holders who worry about inheritance. Tradeoff: contract risk, chain-specific availability.
Decision rule: map your persona’s primary wallet type from Table A onto the tier from Table B. If Table B says “multi-sig mandatory” but Persona 1 (HODLer) says “hardware primary” — combine them. The persona doesn’t override the tier.
Step 4 — Verify Trust Signals (5 Quality Filters)
You’ve narrowed to 2-3 candidate wallet types. Now vet specific products against five filters. A wallet that fails two or more should be rejected, no matter how good the marketing.
Filter 1: Open-Source Code
The wallet’s signing logic should be publicly auditable. Verify on GitHub or a similar host. Closed-source wallets can be honest, but you have no independent way to confirm what they do with your keys. For Tier 3+ portfolios, treat closed-source as a hard reject.
Filter 2: Independent Security Audit
The wallet should have at least one audit from a recognised firm in the last 24 months. Common 2026 names doing wallet and smart-contract security work include Trail of Bits, Halborn, Quantstamp, and OpenZeppelin. Read the actual audit report — “audited by X” with no public report is meaningless. Look at the severity of issues found and whether they were fixed.
Filter 3: Track Record
How long has the wallet been live? How has it handled past incidents? A wallet that has weathered a vulnerability disclosure transparently (paid out a bug bounty, communicated clearly, shipped a fix) is often safer than one that has never been seriously tested. Trezor’s January 2024 support-system breach (66,000 user emails leaked, no private keys exposed) was handled with public disclosure and that pattern matters.
Filter 4: Active Development
Check the GitHub commit history. Healthy wallets ship updates monthly at minimum. A wallet whose last commit was 9 months ago is a red flag — it may be quietly abandoned, leaving you exposed to chain upgrades, browser changes, or new attack patterns.
Filter 5: Bug Bounty Program
The wallet should have a public bug bounty program (Immunefi or HackerOne are common 2026 platforms). Bounty programs signal that the team takes security seriously and that white-hat researchers have an incentive to disclose responsibly rather than sell findings to attackers.
Table C — Trust Signal Checklist (Self-Audit)
| Filter | How to verify | Pass | Fail | N/A |
|---|---|---|---|---|
| 1. Open-source | GitHub repo for signing/key logic | ☐ | ☐ | ☐ |
| 2. Recent audit | Public PDF, ≤24 months old | ☐ | ☐ | ☐ |
| 3. Track record | Years live, incidents handled publicly | ☐ | ☐ | ☐ |
| 4. Active development | Commits within last 90 days | ☐ | ☐ | ☐ |
| 5. Bug bounty | Listed on Immunefi or HackerOne | ☐ | ☐ | ☐ |
A wallet that scores 5/5 isn’t automatically right for you — Steps 1-3 still gate the decision. But 5/5 on trust signals plus the right type for your persona and tier is the combination that survives the migration test.
Step 5 — Test Before Committing ($100 Trial Method)
This is the step most guides skip and most regretful holders wish they’d done.
When we ran this trial across three candidate wallets last quarter, recovery failure was the most common issue we hit — the wallet sent and received fine, but importing the seed phrase to a different device produced a different address in two of the three cases. That’s the kind of surprise you want to discover with $100 at stake, not $50,000.
Before moving any meaningful portion of your portfolio into a new wallet, run a one-week trial with $100 worth of crypto (or whatever amount feels low-stakes to you). The point is to surface UX issues, recovery gaps, and red flags before they cost you real money.
The Trial Checklist
- Send and receive on the primary chain. Move $100 in. Move $50 out. Confirm both transactions land where you expect.
- Switch networks if multi-chain. Add at least one secondary chain you’ll use. Receive a token on it. Many wallets fail at this step quietly — coins arrive but the UI doesn’t show them.
- Connect to a dApp. If you’re a Persona 2 or 3 user, connect to one DEX or DeFi protocol you’ll actually use. Sign a test transaction (not just an approval). Observe how clearly the wallet displays what you’re signing.
- Import a custom token. Add a token that isn’t on the default list. If this requires copy-pasting a contract address from somewhere unsafe, note it.
- Test recovery. Write down the seed phrase or recovery method. Wipe the wallet (or install a fresh copy on a different device). Restore from your backup. If recovery fails, your wallet choice is wrong.
Run the trial for at least 7 days. Use the wallet for everything you’d use it for in production. If anything frustrates you in week one, it will frustrate you for years.
Red Flags During the Trial
- Customer support takes more than 48 hours to respond, or responds via Telegram only (impersonation risk)
- The wallet pushes a forced update mid-trial without changelog
- Fees displayed in the wallet differ materially from on-chain fees
- Recovery requires entering the seed phrase into a web form (this should never happen)
- Token balances render incorrectly or with significant delay
If you hit any of those, the trial has saved you. Pick another candidate from Step 4 and start the trial over.
Step 6 — Quarterly Review Routine
The wallet you pick in 2026 is unlikely to be the right wallet in 2028. Crypto moves too fast. The fix is a 90-day review habit.
The 90-Day Audit
- Re-test recovery. Once a quarter, simulate a recovery on a different device. If the seed phrase is in a fireproof safe and you’ve never restored from it, you don’t know if it works.
- Check incident history. Has your wallet had a vulnerability disclosed? Has a competitor wallet had one that suggests an industry-wide weakness? (For example, the SEC Division of Corporate Finance statement on August 5, 2025, clarifying that ministerial liquid staking activities don’t constitute investment contracts under the Howey test was a reminder that regulatory wind shifts can change which features matter.)
- Verify development activity. Has the GitHub repo gone quiet? If commits stop for 90+ days, start evaluating alternatives.
- Re-rank against your tier. Has your portfolio grown into a higher tier? If yes, upgrade the wallet stack before you regret it.
- Audit approvals. For browser extension users especially, review and revoke unused token approvals quarterly. Tools like Revoke.cash automate this.
The EigenYields slashing event on March 29, 2026 (~$250M in delegator funds redirected through redistributable slashing) and the Kelp DAO bridge exploit three weeks later are recent reminders that DeFi-adjacent wallet usage carries protocol risk on top of wallet risk. Quarterly reviews catch the drift.
Common Decision Mistakes (Anti-Patterns)
We’ve tracked five recurring failure patterns across our reader base, Reddit migration threads, and support-forum incidents. Here are the most common ways the framework gets short-circuited.
Mistake 1: Choosing by Exchange Convenience
“My exchange has a built-in wallet, so I’ll use that.” That’s custody, not a wallet. If the exchange freezes your account, halts withdrawals, or files for bankruptcy, the “wallet” goes with it. Use exchange custody only for funds you’re actively trading.
Mistake 2: Skipping Multi-sig for High Net Worth
If you’re at Tier 4-5 and using a single hardware wallet, you have one point of failure. A device fault, a forgotten passphrase, or a personal emergency (illness, accident) can lock the funds permanently. Multi-sig is annoying to set up. Losing the entire portfolio is worse.
Mistake 3: Trusting Vendor Marketing Over Audits
“Most secure wallet on the market” appears in nearly every wallet’s marketing copy. Read the audit reports instead. A wallet with two recent third-party audits and three published vulnerabilities (each fixed) is provably safer than one with zero audits and zero published vulnerabilities — the second wallet just hasn’t been seriously examined.
Mistake 4: Not Testing Recovery
An untested seed phrase is a hope, not a backup. Run the recovery test in Step 5 before you commit, and again in every quarterly review. The day you actually need recovery is the wrong day to discover that one of your 24 words was misspelled.
Mistake 5: One Wallet for Everything
Active trading and long-term holding have opposite security profiles. Mixing them in one wallet means a phishing approval that drains your trading wallet also drains your retirement. Two wallets — one hot for activity, one cold for treasury — is the minimum for any Tier 3+ user.
Frequently Asked Questions
Is a hardware wallet always best?
No. For a Tier 1 user transacting weekly with $200 of crypto, a hardware wallet adds friction without much marginal security gain — phishing approvals are the bigger risk than key extraction, and a hardware wallet doesn’t protect you from blind-signing a malicious approval. Hardware becomes essential at Tier 2+ when the cost of key compromise outweighs the cost of friction.
How many wallets should I use?
Two is the minimum for Tier 2+ users (one hot for activity, one cold for treasury). Three is reasonable for multi-chain users (add a chain-specific wallet for non-EVM activity). More than four becomes a coordination problem — you’ll lose track of where things are. Multi-sig users count the multi-sig as one wallet regardless of how many signers it has.
Can I trust a free wallet?
Most reputable wallets are free — the business model is on-ramping, swaps, or staking rewards rather than software fees. Free isn’t a red flag. The red flag is opaque: a wallet that doesn’t disclose its revenue model, isn’t open-source, and has no audit. When a wallet is “free + opaque,” your data and behaviour are usually what’s being monetised.
What if my wallet provider goes out of business?
For non-custodial wallets, your funds remain accessible as long as you have the seed phrase or private key — the provider going dark doesn’t change the on-chain state. You’ll need to import the seed into another compatible wallet. This is why we recommend testing recovery into a different wallet during the Step 5 trial: it confirms your seed phrase is portable. For custodial wallets, the provider failing usually means losing access — another reason to keep custodial holdings minimal.
When should I switch wallets?
Five triggers: (1) a security incident specific to your wallet that wasn’t transparently handled, (2) the wallet stops shipping updates for 90+ days, (3) your portfolio crosses a tier boundary the wallet wasn’t designed for, (4) the wallet drops support for a chain or feature you depend on, or (5) the wallet’s parent company changes ownership in a way that affects custody or roadmap. Don’t switch wallets on a whim — every migration has a small risk of losing access. Have a concrete reason.
Conclusion: The Decision Framework, in One Page
The six steps, summarised:
- Identify your use case. Pick the persona (HODLer, trader, DeFi, multi-chain, team).
- Audit your threat model. Match portfolio size and threats to a tier (1-5).
- Match wallet type. Use Tables A and B together to pick the type, not a specific product.
- Verify trust signals. Score candidates against the 5 filters in Table C. Reject anything below 4/5.
- Test before committing. Run a $100, one-week trial. Test recovery on a different device.
- Review quarterly. Re-test recovery, check incidents, re-rank against your tier.
The framework isn’t a magic bullet — wallet security is ultimately a habit, not a product choice. But applying these six steps once will get you a wallet that fits your situation, and applying them every quarter will keep it fitting as your situation changes.
If you found this useful, the linked articles below go deeper into specific wallet categories and the security incidents we’ve referenced. Bookmark this page and revisit it the next time your portfolio crosses a tier boundary.
Continue Learning
- Best Crypto Wallets 2026: Hot vs Cold, Custodial vs Self-Custody
- Hardware Wallet 2026: Trezor vs Ledger vs SafePal vs Tangem Compared
- Best Crypto Wallets 2026: Hot vs Cold vs Multi-sig (Complete Guide by User Persona)
- Best EVM Browser Wallets 2026: MetaMask vs Rabby vs Rainbow vs OneKey vs Frame — Honest Comparison by Use Case
- Protect Your Crypto: 10 Security Rules Every Holder Needs (2026)
- USDT Frozen by Tether: Complete Recovery Guide (2026)
- Crypto Scams in 2026: 7 Types That Stole $14 Billion Last Year
Disclaimer: This article is educational and does not constitute financial, legal, or security advice. Wallet vendors, audit firms, and incident details are referenced as of 2026 and may change. Always verify current security status with the wallet’s official channels before transferring funds. ChainGain receives no compensation from wallet vendors named in this guide; affiliate revenue, if any, comes only from exchange referrals in linked articles.